How to Remotely Wipe Data in Case of Device Theft or Data Misuse
- October 15, 2023
Most progressive businesses today are armed with smartphones, laptops, tablets, rugged devices, and IoT devices (Internet of Things). They are now tasked with the added responsibility of managing all of the mobile devices that are moving their business forward. They need to be able to keep track of all of the devices, data, and information that is being used across their departments and enterprise systems.
Data is becoming the most valuable and informative element for companies, pushing small to large-scale businesses to rethink their mobile device security and management approaches. The loss and misuse of data, corporate as well as client, interrupts workflow, affects customer relationships and damages brand image that may take years to rebuild. It has huge financial implications for the companies, requiring them to pay hefty fines when their data and devices are compromised.
But most businesses tend to overlook device safety in their attempt to improve security and protect their business-critical data. They are busy working on cybersecurity and neglect the threats that are likely to come from the loss or theft of devices. Often, ignoring this vulnerable link in their overall data security strategy has irrecoverable effects on the business and all its future endeavors. Protecting your business devices is one of the most important things you can do. But if you don’t take some simple precautions, you could be handing over a lot of money to electronic pickpockets. The cost of a lost laptop or any device for that matter has far greater consequences than just the cost of the device replacement itself. A research study revealed that the average cost of a lost laptop, including downtime, support, and management time, exceeds $49,000. For small businesses, this kind of loss could spell disaster. Thankfully, just a well-implemented security policy can reduce laptop theft by 85 percent1.
The following blog is meant to be a guide to learn how to protect your business from being the next one to fall victim to device theft and data misuse.
What Is Remote Wipe Out?
A remote wipe is just like a sugar pill. No, really! It’s a security feature that allows companies to send a command that deletes data if a device has been lost or stolen – say, a smartphone – so that if the device (or the information stored on it) falls into the wrong hands, the sugar pill will somehow make the data go away remotely. It’s also used to remove data from devices in case of device malfunctions, changes in end-user or administrators, and when devices cannot be accessed physically to remove data.
Importance of Remote Wipeout
Remotely wipe Android is easily accessible to businesses as a part of the Mobile Device Management (MDM) solution that allows IT admins to wipe out all data and memory and leave the device unusable. The MDM tool can be configured to remove data from devices at the command of IT admins from the cloud. CubiLock MDM solution offers a suite of security features that allow businesses to secure mobile devices and enforce policies for data protection and remote wipe out. Remote data wipeout addresses a range of threats to confidential and sensitive enterprise data, such as:
- Data theft: Employees knowingly infiltrate companies’ data and information to sell it to external third parties or attackers.
- Device loss: Devices used remotely or inside office premises are lost or misplaced due to various reasons.
- Malware and Viruses: Devices are exposed to malignant malware, viruses, hackers, and attackers via mobile apps, websites, and other potential vulnerabilities.
- Change in device owner: Employees decide to quit or there is a need for end-user/ device owner replacement.
CubiLock MDM not only allows complete device reset but also remotely wipe Android data, where employers can remove corporate data from employees’ personal devices, remove apps and the data within, and much more flexibility to cater to the unique requirements and needs of your business.
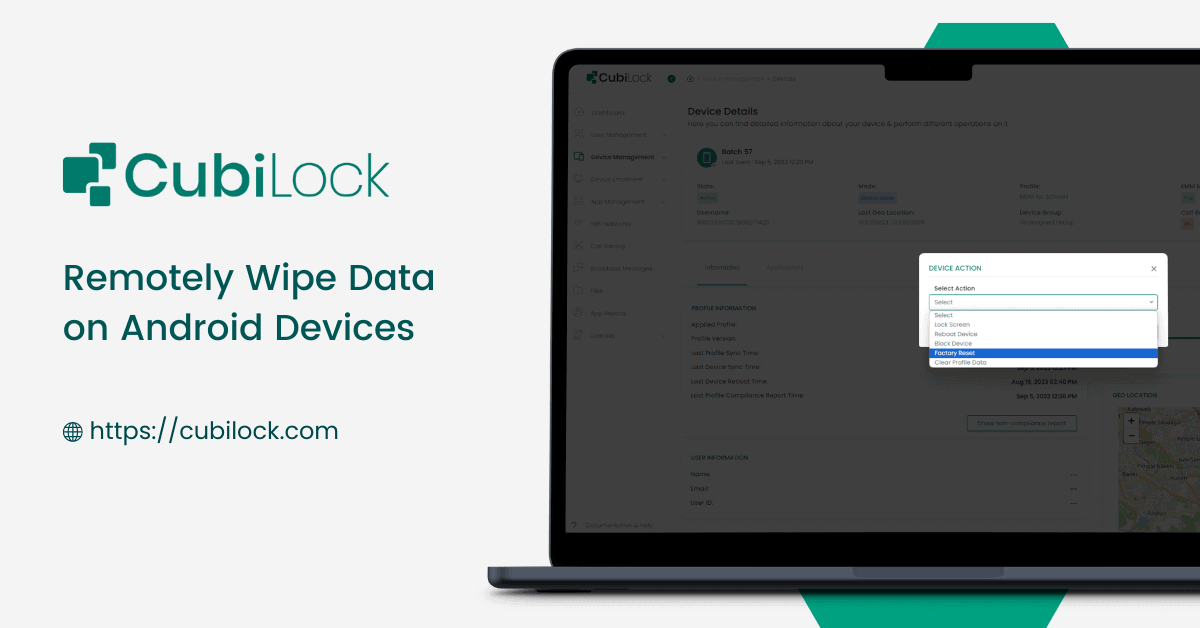
Steps to Remotely Wipe Android devices With Cubilock MDM:
- Sign up and enroll your Android devices OR log in to the CubiLock portal.
- Go to the Device List page, under Device Management.
- On the top-right of the page, click on Select in the Action dropdown menu.
- For selective data wipeout, Choose the preferred action from:
– Lock Screen
– Reboot Device
– Block Device
– Factory Reset
– Clear Profile Data
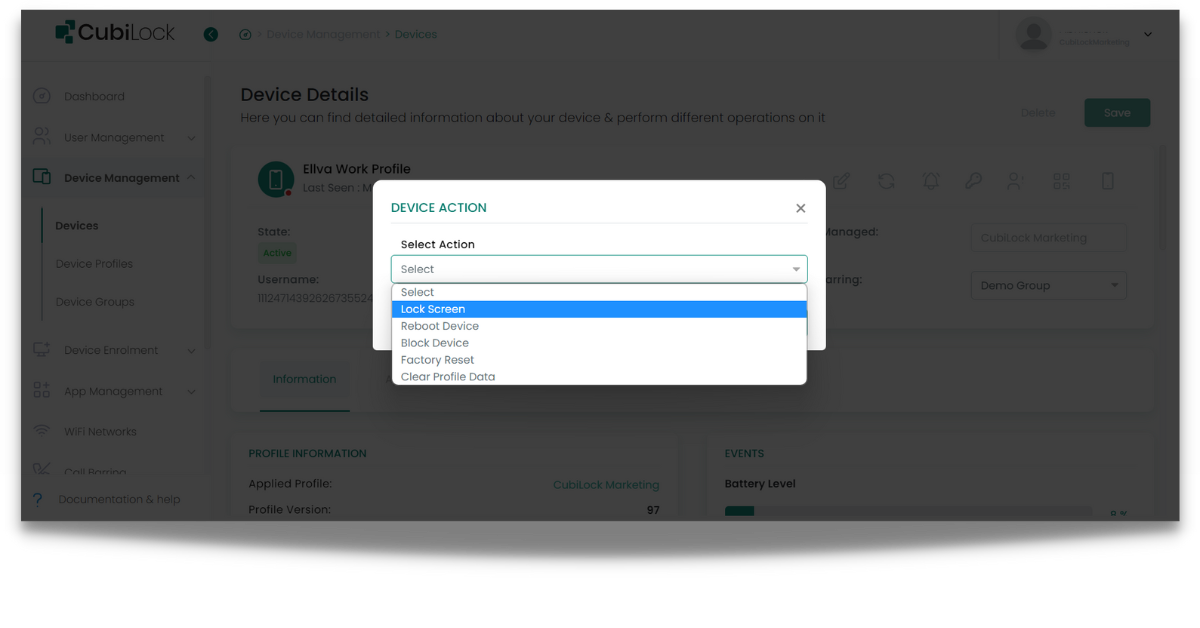
- For complete data wipeout, Choose Factory Reset.
- Save all changes. The device will go through the selective wipeout OR factory reset.
With the rising popularity of mobility, it’s important to think about the different ways your data could be compromised, and then take additional steps to protect the sensitive data in their possession to prevent those scenarios from happening. One of the most common ways that data is compromised is through loss or theft. Whether you have a full-time IT staff or you’re the IT department for your business, the CubiLock MDM solution provides robust device management features for setting and enforcing policies for your devices. It enables remote wipe in the event of a security breach with easy and simple steps without adding any more pressure on IT admins. CubiLock will be an undeniably important asset for your business to keep your data and device security in check.

Apart from being a true sushi enthusiast, Sadichha (Aka SSH) is a content writer and blogger at CubiLock. She is passionate to enchant everything boring and nitty gritty about technology through her writings for her readers to enjoy and learn from at the same time. When she is not at her desk crafting content, you can catch her occupied with her cat.