Understand the Difference Between MDM, EMM, and UEM
- October 15, 2023
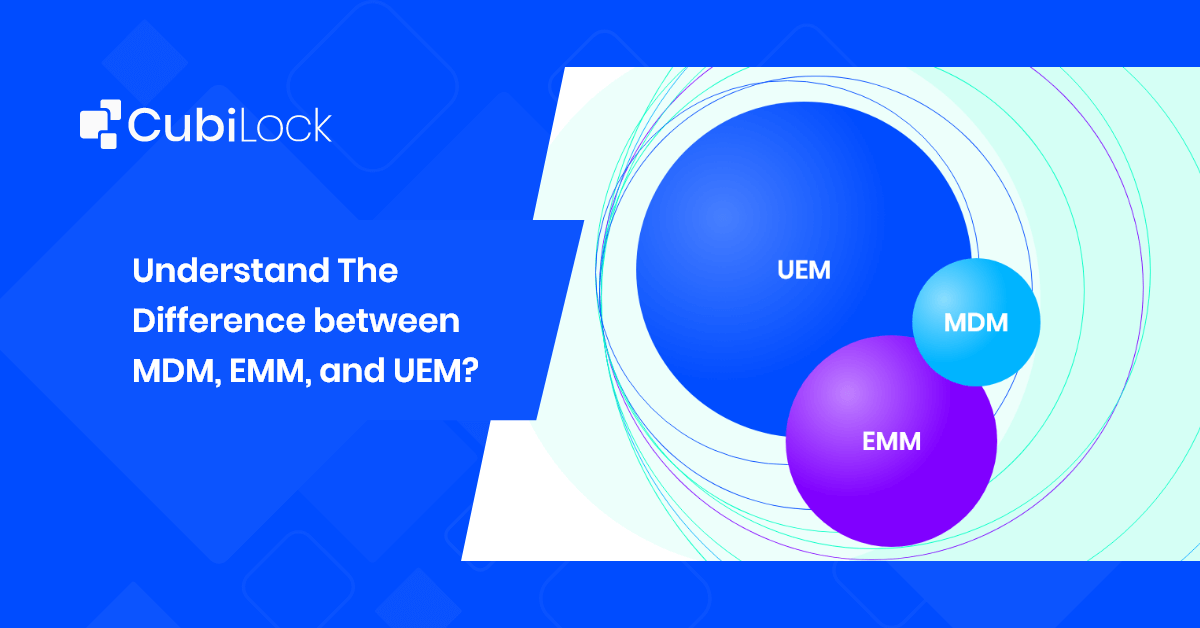
Mobile Device Management (MDM), Enterprise Mobility Management (EMM), and Unified Endpoint Management (UEM) are some of the recurring names in the mobility management space. These terms are thrown around interchangeably by enterprises when in reality they have key scalability and control differences. However, they don’t have to be as confusing as they might seem. Technological fluency is not the mother tongue of most enterprises unless you specialize in it, but technology is something every enterprise needs to foster so here we have laid the basics of mobility acronyms such as MDM EMM and UEM, and the key differences between them for you to make an informed decision on which mobility management solution is the right fit for your business needs.
Deploying the wrong mobility approach not only stifles the growth and progress of a company but kills employee morale as well. It takes the business backward rather than expand its capabilities to manage, secure and control endpoints that are connected to the extensive network. Mobility management has a broader scope that encompasses MDM, EMM, and UEM which overlap each other under its umbrella. In simple terms, these are just evolutionary phases of mobility management that have evolved to meet the changing business requirements.

Difference between MDM, EMM, and UEM
Businesses always strive to make their organizations more effective and efficient. Apart from choosing the right technology, organizations can take recourse to different mobility management techniques for this purpose. In this article, we are going to discuss the three device management approaches that have become popular in the recent past.
Mobile Device Management (MDM)
MDM detects and neutralizes device malfunctions and data threats ensuring lower device downtime and a longer device life cycle for a business. It efficiently mitigates data privacy and device security risks involved in deploying devices and distributing files and information. The hassle of enrolling all interconnected devices and prohibiting their misuse cannot be manually managed by any company regardless of its size. This issue is tackled with its wide range of features availed by a good MDM solution.
Mobile Device Management (MDM) is a mobility management tool that offers full device deployment, management, security, and control on smartphones and tablets, either personally owned or corporate-issued. It focuses on the management of device-led operations that predominantly run on Android or iOS. It allows companies to provision quick enrollment, policy configuration, location tracking, kiosk mechanism, device, and data security, and remote wipe out as its prominent features. IT teams can profile employee devices according to their tasks and job profile and then push specific applications and websites relevant to the work purpose of the devices. MDM supports the use of personally owned devices (Bring Your Own Device/BYOD) to cater to employees that need flexibility, corporate devices such as self-service kiosks, Android single app mode or multi-app mode kiosks, and mPOS (mobile Point Of Sale) devices.

Enterprise Mobility Management (EMM)
The exponential growth of smartphones lead to bigger gaps in data security and device management that needed to be filled which in turn led to the expansion of mobile device management (MDM) to a broader suite of features, known as Enterprise Mobility Management (EMM). EMM solutions encompassed all MDM features along with additions of:
- Mobile application management (MAM)
- Mobile content management (MCM)
- Mobile security management (MSM)
- Containerization (BYOD)
- Identity and access management (IAM)
The intricate features of EMM enable enterprises to create a harmonious balance of user experience, and productivity and enhance endpoint security. Where MDM falls short, EMM provides its comprehensive solution that helps cubicle workers and remote workers, all the same, to collaborate, receive enterprise resources, and deliver on their commitments through a seamless interface.
- Mobile application management (MAM) singularly focuses on the management and control of specific business applications. MAM is useful to create your own enterprise app store, push, install, and update work-relevant apps on devices and configure them with particular business policies so the devices can stay on top at all times.
- Mobile content management (MCM) is more of a security technology that provides safe access to corporate content and data on all endpoints. It is ideally used to push, access, store, and distribute content from the internal repository of the company.
- Containerization is the most effective system for BYOD. It allows personal and corporate data to co-exist in a single device while ensuring they are segregated at all times with separate encrypted containers that keep business data protected from data leaks and other multiple vulnerabilities.
- Identity and access management (IAM) uses a security framework to identify and authenticate users to provide access privilege for smartphones, laptops, rugged devices, software applications, files, data, and websites. IAM provides full-proof security and mitigates sophisticated cybersecurity risks and data breaches.
Unified Endpoint Management (UEM)
MDM and EMM solutions have all the tools to manage mobile devices while Unified endpoint management (UEM) takes it a step further and manages other endpoints such as PCs, rugged devices, IoT devices, wearables, etc through a single console. UEM encapsulates MDM and EMM and other mobility management functions to cater to the needs of enterprises with complex management needs or a variety of endpoint deployments.
UEM tools can manage any platform and device with its full set of features that provides a secure environment for companies to manage, control, and track all endpoints. The flexible, simplistic, and holistic nature of a unified dashboard in a Unified endpoint management solution makes it a complete package approach for all types of businesses.
Also Read: MDM Checklist For IT Admins
MDM solutions are dedicated to device-led functions, while EMM covers corporate as well as personal device management with a suite of other features whereas UEM unlocks greater management potential with enhanced security and management of all types of endpoints. Now all your business needs to assess simple questions such as:
- the size of your business
- use cases of the devices
- tasks of everyday employees
- types of endpoints deployed
- Number BYOD or corporate devices
Understanding and analyzing these simple yet evident differences between MDM, EMM, and UEM mobility management tools helps you make correct decisions for the growth of your business.
EMM vs MDM: Unveiling the Differences and Synergies
Enterprise Mobility Management (EMM) and Mobile Device Management (MDM) are two vital pillars of modern mobile management strategies, each with its own set of features, capabilities, and areas of focus. Understanding their differences and synergies is essential for organizations aiming to effectively manage their mobile devices and ensure the security of sensitive data.
Synergies: Working Hand in Hand
While MDM and EMM have distinct focuses, they can work in harmony to deliver a robust mobile management strategy. EMM solutions like CubiLock incorporate MDM functionalities as a foundational component. By integrating MDM and EMM framework, organizations can harness the benefits of both approaches. This synergy allows for streamlined device management alongside the management of apps, content, and identities. Consequently, organizations can strike a balance between security and productivity, catering to a mobile workforce’s dynamic needs.
The choice between EMM and MDM or comparing EMM vs MDM depends on an organization’s specific requirements and goals. EMM offers a broader perspective by incorporating various aspects of mobile management, while MDM excels in centralized device control. By understanding their differences and synergies, organizations can tailor their mobile management strategies to enhance both security and efficiency in today’s mobile-centric business landscape.
If you are looking for a one-stop approach for your management strategies or concerns, the simple and effective interface of CubiLock can help mitigate the challenges of your enterprise mobility drive.

Apart from being a true sushi enthusiast, Sadichha (Aka SSH) is a content writer and blogger at CubiLock. She is passionate to enchant everything boring and nitty gritty about technology through her writings for her readers to enjoy and learn from at the same time. When she is not at her desk crafting content, you can catch her occupied with her cat.